UPDATE: Snapchat and Third-Party Applications1
The original Snapchat library this post was made for is outdated. Liam Cottle has provided an up to date Snapchat PHP library with captcha support.
Myself and Graham Smith are providing a Snapchat library for Golang with captcha support. This post will remain here as an archive/reference.
Use at your own risk.
Last updated: 02 July 2017 11:21:05
For those who are unfamiliar with Snapchat, it’s an app that lets you share photos and videos with people, (in particular your friends) which “disappear” forever when viewed.
(Well, you can get the “deleted” image by replaying the snap.)
There has been a lot of buzz around the new “snaptcha” system that Snapchat implemented into their app.
“Snaptcha” is a clever play on of the word CAPTCHA used as a challenge to prevent spambots from accessing a service. You may have already seen it in action when signing up to a website.
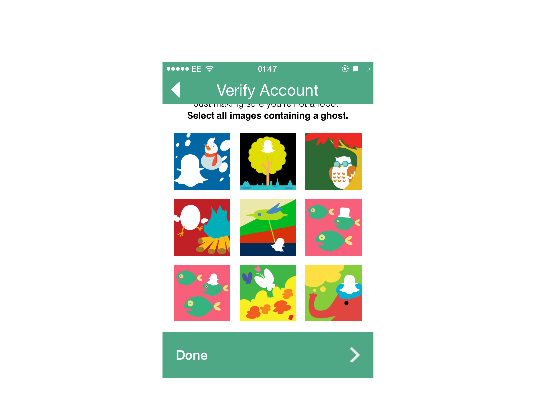
Except, Snapchat’s version is just a bunch of computer generated images.
Graham Smith made an interesting blog post about Snapchat’s security. He claimed to have written a “Snaptcha Liberation” script, and plans not to release the code. So I decided to take a stab at it.
This post is aimed at people who want to bypass Snapchat’s CAPTCHA (or ‘Snaptcha’).
We will be using example credentials for this post.
Warning: Technical content ahead!
In every HTTP(S) request you send to Snapchat, you must include two parameters:
req_token and timestamp.
I’m not going to go through how to generate these parameters, but you can see how to do so here.
Next, for the sake of brevity in this blogpost, we are going to use SC_URL as the Snapchat URL.
where SC_URL = https://feelinsonice-hrd.appspot.com
/loq/register
(The /loq/ endpoint is new but the same as /bq/register)
First of all, go ahead and send a POST request as normal to:
{SC_URL}/loq/register
have a look at the link above to find out the POST parameters for this endpoint.
If successful, you should get this response from the server:
{
"email": "[email protected]",
"should_send_text_to_verify_number": false,
"snapchat_phone_number": "+447937983869",
"auth_token": "539e0ed0-81b7-4a81-9367-3047b16e66e7",
"logged": true
}
/loq/register_username
Next, this part you need to enter a desired username
send a POST request to:
{SC_URL}/loq/register_username
Parameters:
username = your email (e.g. [email protected])
selected_username = (eg. snaptchauser)
timestamp = the current timestamp.
req_token = your request token.
If successful, you should get a 200 and from the server and a large JSON output from the server.
...
"verification_needed": {
"prompt": "Select all images containing a ghost.",
"type": "needs_captcha"
}
...
But you would still need to verify your account in order to access it.
/bq/get_captcha
Next, you need the email you sent earlier to be your username.
send a GET request to:
{SC_URL}/bq/get_captcha
Parameters:
username = your username (eg. snaptchauser)
timestamp = the current timestamp.
req_token = your request token.
if successful, you should get a .zip file from the server. At this point, Snapchat sends over a .zip to you. To continue to register, you need the correct captcha_id. To get this you need to dump the Content-Disposition response header.
It should look like this in your response header.
attachment;filename=snaptchauser~1411327319782.zip
You need it to look like this:
snaptchauser~1411327319782
The above is your captcha_id
/bq/solve_captcha
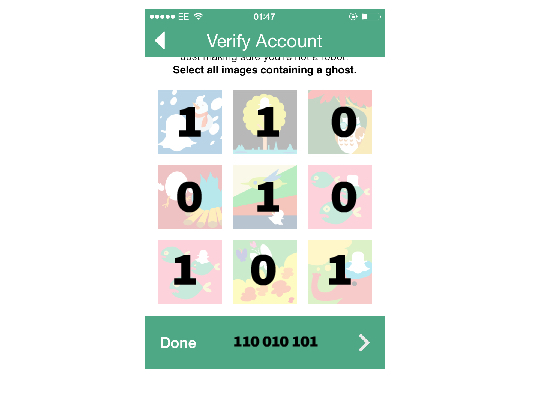
Lastly, Snapchat’s captcha system requires two new parameters.
captcha_id = The string you dumped earlier.
captcha_solution = The 9-digit long binary solution. eg. 101100010
This is where you "Select all images containing a ghost."
For instance:
1 = ghost
0 = no ghost.
This relates closely to the grid shown below.
Now send a POST request to:
{SC_URL}/bq/solve_captcha
captcha_solution = (eg. 110000000)
captcha_id = (eg. snaptchauser~1411327319782)
username = Your username (eg snaptchauser)
timestamp = The current timestamp.
req_token = your request token.
If you get a 403, check your captcha_solution if it matches the images accordingly in the zip file. If successful, you should get a 200 from the server.
If you have got this far, you have successfully bypassed the captcha and registered a Snapchat account!
Credit goes to these guys:
Graham Smith for finding vulnerabilities in the Snapchat app.
Gibson Security for extensively documenting the Snapchat API.
Oliver Martinez for his proven solution. Plus his effort in porting Snapchat to the Blackberry 10.